Understanding the critical nature of ‘POC Login’ efficiency in today’s fast-paced digital landscape can dramatically enhance both user experience and operational efficiency. A POC Login (Proof of Concept Login) offers a strategic gateway for organizations to validate authentication methods before widespread implementation. This guide delves into expert perspectives with practical insights, evidence-based statements, and real-world examples to streamline your POC Login processes.
Key Insights
- Primary insight with practical relevance: Implement a streamlined POC Login protocol to expedite validation processes.
- Technical consideration with clear application: Utilize adaptive authentication mechanisms to bolster security during POC Login.
- Actionable recommendation: Start with a pilot program for POC Login to refine and enhance security protocols.
The Importance of Quick POC Login Validation
The speed and efficiency of a POC Login are paramount. With rapid technological advancements, the time-to-market for authentication solutions is shrinking. Efficient POC Login not only expedites the validation phase but also minimizes potential delays in implementing new authentication systems. When companies can swiftly test and validate authentication methods, it helps to ensure that the systems meet stringent security standards and are tailored to user needs.Adaptive Authentication in POC Login
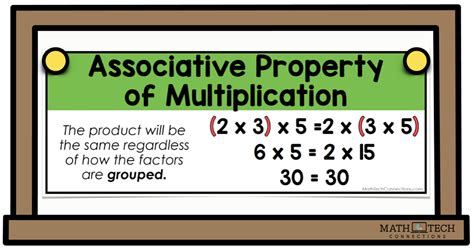
Adaptive authentication plays a crucial role in the POC Login process. By integrating adaptive authentication, organizations can dynamically adjust security measures based on user behavior and context. This approach helps in identifying potential threats in real-time, ensuring a robust security framework during the POC phase. For instance, companies employing machine learning algorithms can analyze user patterns to detect anomalies and adjust authentication levels accordingly, thus providing both security and user convenience.Adaptive authentication goes beyond simple passcode verification. It incorporates multi-factor authentication (MFA), biometric verification, and behavioral analytics. The real strength of adaptive authentication lies in its ability to respond to new threats on-the-fly, maintaining a security posture that evolves with technological changes. Organizations can use such advanced authentication methods to create a more secure and efficient POC Login, reducing friction and increasing user trust.
What are the benefits of adaptive authentication during POC Login?
Adaptive authentication provides a dynamic and responsive security mechanism that adjusts to user behavior and potential threats in real-time. This not only improves the security of the POC Login process but also enhances user experience by minimizing unnecessary security challenges.
How can a pilot program enhance POC Login efficiency?
A pilot program for POC Login allows organizations to test new authentication methods on a smaller scale before full implementation. This iterative approach helps in identifying potential issues, refining processes, and ensuring that the system is both secure and user-friendly.
In conclusion, the efficient handling of POC Logins through streamlined validation processes and adaptive authentication mechanisms can significantly enhance both security and user satisfaction. By focusing on these key areas, organizations can ensure that their authentication systems not only meet but exceed the evolving demands of the digital age.