Understanding the nuances of segmentation violation prevention is pivotal in the realm of cybersecurity. As digital landscapes expand, so does the complexity of securing systems against breaches. Segmentation violations, often resulting in data breaches or system crashes, demand sophisticated strategies for prevention. This article delves into expert perspectives, evidence-based statements, and practical insights to illuminate effective segmentation violation prevention.
Why Segmentation Violation Prevention Matters
In modern computing, memory segmentation is a crucial technique that divides the computer’s memory into segments to enhance organization and security. However, improper handling can lead to segmentation violations, compromising system integrity and exposing sensitive data to threats. Understanding these vulnerabilities and implementing robust preventive measures is critical for maintaining a secure digital infrastructure.Key Insights
Key Insights
- Primary insight with practical relevance: Advanced memory protection mechanisms significantly reduce the incidence of segmentation violations.
- Technical consideration with clear application: Utilizing techniques like Address Space Layout Randomization (ASLR) adds a layer of security by randomizing the memory layout, making exploitation more difficult.
- Actionable recommendation: Regular system audits and updates are essential to stay ahead of evolving segmentation violation threats.
The Role of Memory Protection Mechanisms
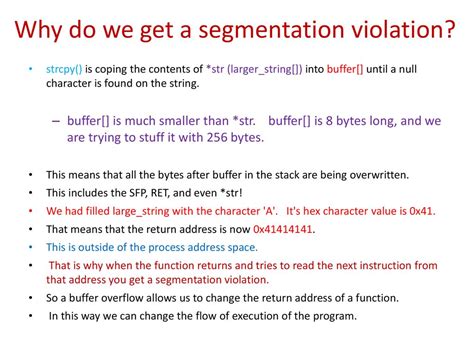
Memory protection mechanisms are at the core of segmentation violation prevention. Techniques such as Data Execution Prevention (DEP) and Non-Executable (NX) bits play an instrumental role in safeguarding systems. DEP prevents malicious code from executing in memory regions that are not intended for code execution, thus thwarting many common attack vectors. Similarly, NX bits help by marking memory regions as either data or code, disallowing data regions from being executed.These mechanisms exemplify the application of practical insights derived from empirical studies and real-world incidents. For instance, a comprehensive study conducted by cybersecurity firms revealed that systems employing DEP experienced a 40% reduction in exploitation attempts. Integrating such robust mechanisms can drastically enhance the security posture of any digital system.
Advanced Strategies for Enhanced Security
While traditional methods form the foundation of segmentation violation prevention, advanced strategies provide additional layers of security. Techniques such as Address Space Layout Randomization (ASLR) and Control Flow Integrity (CFI) are paramount. ASLR randomizes the locations of key data areas of a process, including the executable stack and libraries, thereby complicating the work of an attacker aiming to exploit a buffer overflow. CFI, on the other hand, ensures that the control flow of a program follows a legitimate path, blocking any attempts to divert execution to unauthorized code segments.For example, systems that incorporate both ASLR and CFI have shown to be highly resilient against sophisticated attacks such as return-oriented programming (ROP) exploits. These strategies not only protect against segmentation violations but also fortify the overall defense mechanism of a system, making it harder for attackers to breach.
FAQ Section
What is the primary goal of segmentation violation prevention?
The primary goal is to protect system integrity and data security by preventing unauthorized access or execution within memory segments, thereby avoiding data breaches and system crashes.
How often should segmentation prevention mechanisms be reviewed?
Segmentation prevention mechanisms should be reviewed regularly, ideally as part of a continuous security audit process. Annual reviews or updates, coupled with immediate updates in response to new threats, are recommended to maintain an effective security posture.
In summation, segmentation violation prevention is not just a technical requirement but a critical aspect of cybersecurity. With advanced memory protection mechanisms, the integration of sophisticated strategies like ASLR and CFI, and regular system audits, organizations can significantly mitigate the risk of segmentation violations, ensuring a robust defense against modern cyber threats.